Metasploit is a free, open-source framework used by security professionals and hackers alike to test the security of computer systems. It was originally created as a penetration testing tool, but has since evolved into a versatile platform that can be used for a variety of security tasks, including vulnerability assessment, exploit development, and intrusion detection.
Hackers use Metasploit to identify and exploit vulnerabilities in computer systems. They do this by running the framework’s modules, which are scripts that automate various types of attacks. For example, a hacker may use a Metasploit module to launch a remote code execution attack, in which malicious code is run on a target system. This can allow the attacker to gain control over the targeted system, access sensitive data, or use it as a stepping stone to attack other systems.
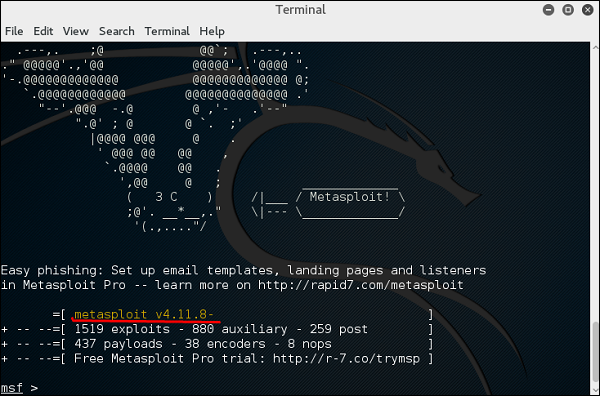
One of the key advantages of Metasploit is its large repository of exploits and modules. The framework is constantly updated with new modules and exploits, making it a valuable resource for hackers who are looking for new ways to penetrate systems. Additionally, Metasploit’s modular design allows hackers to easily customize and extend the framework to fit their specific needs.
However, it’s important to note that Metasploit can be used for both malicious and ethical purposes. Security professionals use the framework to test the security of their own systems, identify vulnerabilities, and develop patches and remediation strategies. This helps to prevent hackers from exploiting these vulnerabilities and protects sensitive data and systems from harm.
In conclusion, Metasploit is a powerful tool that can be used by both hackers and security professionals. While it can be used for malicious purposes, it is also a valuable resource for those working to improve the security of computer systems. Whether you’re a hacker or a security professional, understanding Metasploit and how it works is an important aspect of keeping systems secure.
Leave a Reply
You must be logged in to post a comment.